Analysis at the intersection of security, privacy and infrastructure
Security, Privacy and Infrastructure Insights
From Patch to Breach: Why Speed and Convenience Continue to Undermine Security
What the MOVEit Breach Still Teaches Us About Security In cybersecurity, the most damaging incidents rarely begin with sophisticated attacks. More often, they start with something far less dramatic: a trusted system, widely adopted, quietly exposed. The exploitation of the MOVEit Transfer...
Security by Design, Not by Convenience: A Practical Perspective for Modern Infrastructure
Modern systems are built for speed, scale and ease of use, but when convenience becomes the design priority, security and privacy are usually the first principles to bend. There is a quiet assumption behind much of modern technology: if something feels convenient, it must also be acceptable....
Why Cheap Shared Hosting Is a False Economy
The Illusion of Cheap Hosting Cheap shared hosting is often marketed as the perfect starting point for small businesses and personal projects. For just a few pounds per month, hosting providers promise websites that are fast, reliable, and simple to manage. The value proposition seems obvious....
My Security and Privacy-First Hosting Philosophy
My Security and Privacy-First Hosting Philosophy Security and privacy in hosting are often treated as add-ons - features you enable once the real work is done. I see it differently. Hosting is a chain of trust, and every link is an opportunity either to reduce risk or quietly accumulate it. My...
Scammer steals $1.5 million from Baltimore by spoofing city vendor
The City of Baltimore made more than $1.5 million in fraudulent payments to a scammer who successfully spoofed a vendor and tricked city employees into changing the contractor’s bank account information, the city’s inspector general said. In a post mortem of the incident, Baltimore...
Attackers Abuse Velociraptor Forensic Tool to Deploy Visual Studio Code for C2 Tunneling
Cybersecurity researchers have called attention to a cyber attack in which unknown threat actors deployed an open-source endpoint monitoring and digital forensic tool called Velociraptor, illustrating ongoing abuse of legitimate software for malicious purposes. "In this incident, the...
Student Loan Breach Exposes 2.5M Records
2.5 million people were affected, in a breach that could spell more trouble down the line. EdFinancial and the Oklahoma Student Loan Authority (OSLA) are notifying over 2.5 million loanees that their personal data was exposed in a data breach. The target of the breach was Nelnet...
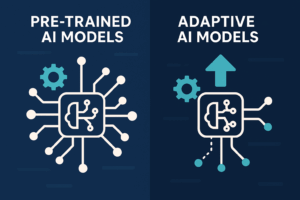
The Hidden Weaknesses in pre-trained AI models vs. adaptive AI models
If you're evaluating AI-powered SOC platforms, you've likely seen bold claims: faster triage, smarter remediation, and less noise. But under the hood, not all AI is created equal. Many solutions rely on pre-trained AI models that are hardwired for a handful of specific use cases. While that...
Why DIY Website Builders Are More Trouble Than They’re Worth
We all know a website is essential for any modern business. It’s your shopfront, your business card, and your voice — all rolled into one. Potential clients form first impressions in seconds, and your website plays a massive part in that. So when platforms promise you can “build a professional...
How much does a website cost?
This is one of the most common questions I get asked — and believe me, you're not the only one Googling it. But the truth is: it's not a simple one-size-fits-all answer. Think of it like planning a new kitchen. You could pop down to the nearest big box store for a flat-pack budget job, or you...
Business Case for Agentic AI SOC Analysts
Security operations centers (SOCs) are under pressure from both sides: threats are growing more complex and frequent, while security budgets are...
Student Loan Breach Exposes 2.5M Records
2.5 million people were affected, in a breach that could spell more trouble down the line. EdFinancial and the Oklahoma Student Loan Authority...
Why DIY Website Builders Are More Trouble Than They’re Worth
We all know a website is essential for any modern business. It’s your shopfront, your business card, and your voice — all rolled into one....
Security by Design, Not by Convenience: A Practical Perspective for Modern Infrastructure
Modern systems are built for speed, scale and ease of use, but when convenience becomes the design priority, security and privacy are usually the...
UK ransomware costs significantly outpace other countries
UK organisations hit by ransomware attacks paid much higher ransoms than in other countries over the past 12 months, according to study British...
My Security and Privacy-First Hosting Philosophy
My Security and Privacy-First Hosting Philosophy Security and privacy in hosting are often treated as add-ons - features you enable once the real...