Modern systems are built for speed, scale and ease of use, but when convenience becomes the design priority, security and privacy are usually the first principles to bend.
There is a quiet assumption behind much of modern technology: if something feels convenient, it must also be acceptable.
Single-click logins. Persistent sessions. Auto-filled credentials. Deeply integrated platforms that promise to “just work”. None of these features are inherently reckless. In fact, most were introduced for sensible reasons - to reduce friction, support adoption and make systems easier to use. That is the trap. Risk rarely arrives looking dramatic. More often, it enters politely, disguised as efficiency.
For security, privacy and infrastructure professionals, that trade-off is becoming harder to ignore. The issue is not convenience itself. The issue is what happens when convenience becomes the default design priority, while security and privacy are left to catch up afterwards.
That pattern now shows up across cloud estates, identity architectures and data-handling practices. According to Verizon’s 2025 Data Breach Investigations Report, credential abuse accounted for 22 per cent of leading initial attack vectors, showing how often attackers succeed by targeting identity pathways rather than breaking through hardened infrastructure (Verizon, 2025). IBM’s Cost of a Data Breach Report 2025 also found that the global average cost of a data breach was USD 4.44 million, a reminder that weak design decisions do not stay theoretical for long (IBM, 2025).
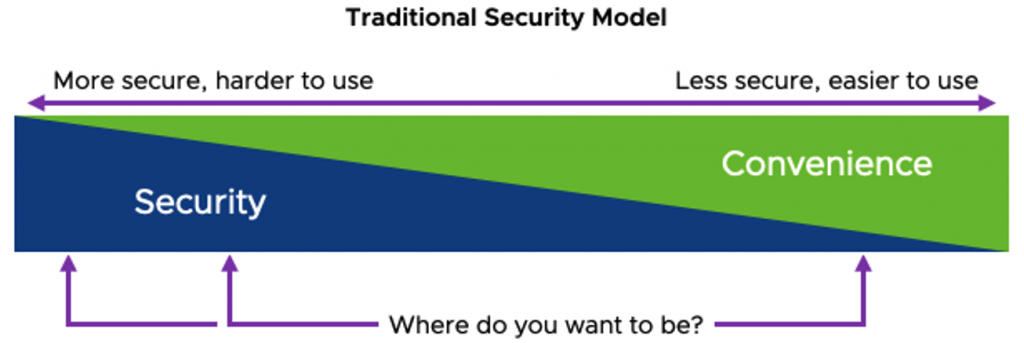
The more convenience becomes the dominant design goal, the more likely security controls are to become reactive rather than foundational.
The uncomfortable truth is that convenience scales faster than control. New services can be deployed in days. Integrations can be switched on in hours. Governance, assurance and privacy review usually take longer - and are often invited in after the furniture has already been arranged.
That is where the real problem begins. Security stops being a design principle and becomes a compensating control. Privacy stops being intentional and becomes a compliance exercise. By then, the organisation is no longer deciding whether convenience should shape the system. It already has.
| Design choice | Short-term benefit | Long-term security or privacy cost |
|---|---|---|
| Persistent logins | Faster access | Greater exposure to session theft |
| Deep SaaS integration | Better workflow efficiency | Reduced visibility across data flows |
| Broad data collection | More analytics and personalisation | Increased privacy risk and data exposure |
| Minimal authentication friction | Improved user adoption | Higher likelihood of credential abuse |
Convenience-led decisions often create delayed security and privacy costs.
Structural Analysis and Emerging Attack Surfaces
The tension between convenience and security is not simply behavioural. It is architectural.
Modern digital infrastructure has evolved toward highly interconnected ecosystems. Cloud platforms, SaaS environments, identity providers and data pipelines now operate as tightly coupled systems rather than isolated environments. This architectural shift has delivered extraordinary operational flexibility. It has also quietly expanded the potential attack surface.
Historically, infrastructure security focused on perimeter defence. Networks were segmented, internal systems were trusted and external actors were filtered through layered controls. That model has largely dissolved in contemporary environments. Remote work, distributed cloud services and third-party integrations mean that the traditional network perimeter now holds far less significance than identity itself.
Today, identity has effectively become the new security boundary.
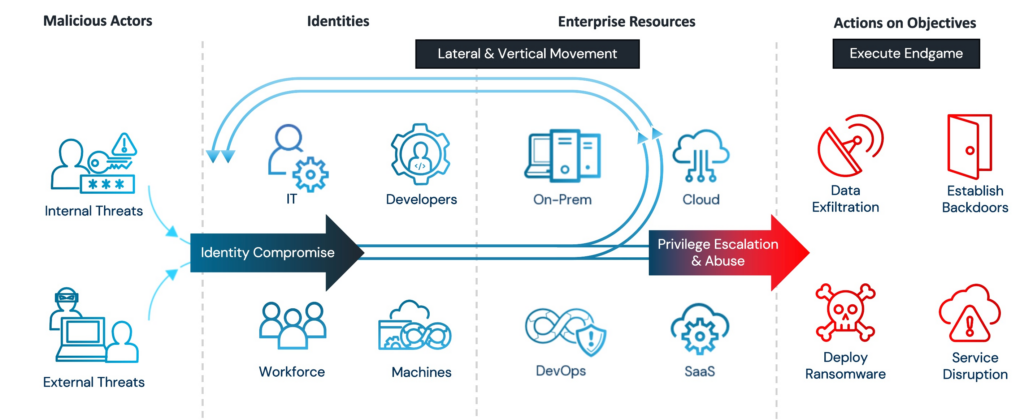
Rather than breaking through hardened infrastructure, attackers increasingly exploit the authentication layer that connects users, applications and data. The mechanisms that make systems convenient - persistent authentication sessions, simplified login workflows and federated identity models - also create pathways that can be abused when identity credentials are compromised.
Research from Microsoft’s Digital Defense Report indicates that more than 99.9 per cent of automated account compromise attempts are blocked when multi-factor authentication is enabled, demonstrating how central identity protection has become to modern security posture (Microsoft, 2023).
However, identity systems also illustrate the convenience paradox particularly well. Organisations often introduce federated login models, single sign-on systems and cross-platform authentication to reduce user friction. These technologies are extremely valuable when implemented correctly. Yet they also concentrate risk. A single compromised identity token may grant access across multiple services simultaneously.
In other words, the convenience that simplifies user experience can also simplify attacker movement.
This is not necessarily a flaw in the technology itself. It is a reflection of how interconnected infrastructure now behaves. Security architecture must account not only for system vulnerabilities but also for the relationships between systems.
When convenience accelerates integration faster than governance can adapt, visibility becomes the real challenge. According to IBM’s Cost of a Data Breach Report, the average time to identify and contain a breach was 277 days, demonstrating how complex environments can slow detection and response (IBM Security, 2023).
In many cases, breaches are not the result of a single catastrophic failure. They are the cumulative result of small design decisions that prioritised usability over architectural clarity.
| Security Model | Primary Security Boundary | Common Attack Focus | Typical Weakness |
|---|---|---|---|
| Traditional perimeter security | Network perimeter | Network exploitation | Poor internal segmentation |
| Cloud and SaaS environments | Identity systems | Credential theft, phishing | Over-privileged identities |
| Federated identity environments | Identity providers | Token abuse and session hijacking | Concentrated access risk |
Privacy and Security Implications
When convenience begins to dominate design decisions, the consequences are rarely immediate. Instead, they accumulate gradually across infrastructure, identity systems and data governance practices.
One of the most significant impacts is the quiet expansion of data exposure. Systems optimised for user convenience frequently collect more information than is operationally necessary. Behavioural analytics, integrated services and automated personalisation often require continuous data flows between platforms. While these capabilities can deliver genuine value, they also increase the number of locations where sensitive information may reside.
From a privacy engineering perspective, the safest data is the data that is never collected.
This principle aligns closely with regulatory frameworks such as the General Data Protection Regulation (GDPR), which promotes the concept of data protection by design and by default. Organisations are expected to minimise personal data processing wherever possible and embed privacy considerations into system architecture rather than applying them retrospectively (European Commission, 2016).
The challenge arises when convenience-driven services encourage the opposite behaviour. Data collection expands because it enables better user experience, deeper analytics or more seamless integrations. Over time, the volume of stored information grows faster than the organisation’s ability to monitor or protect it.
Security teams then find themselves defending an environment that has become increasingly complex without deliberate design.
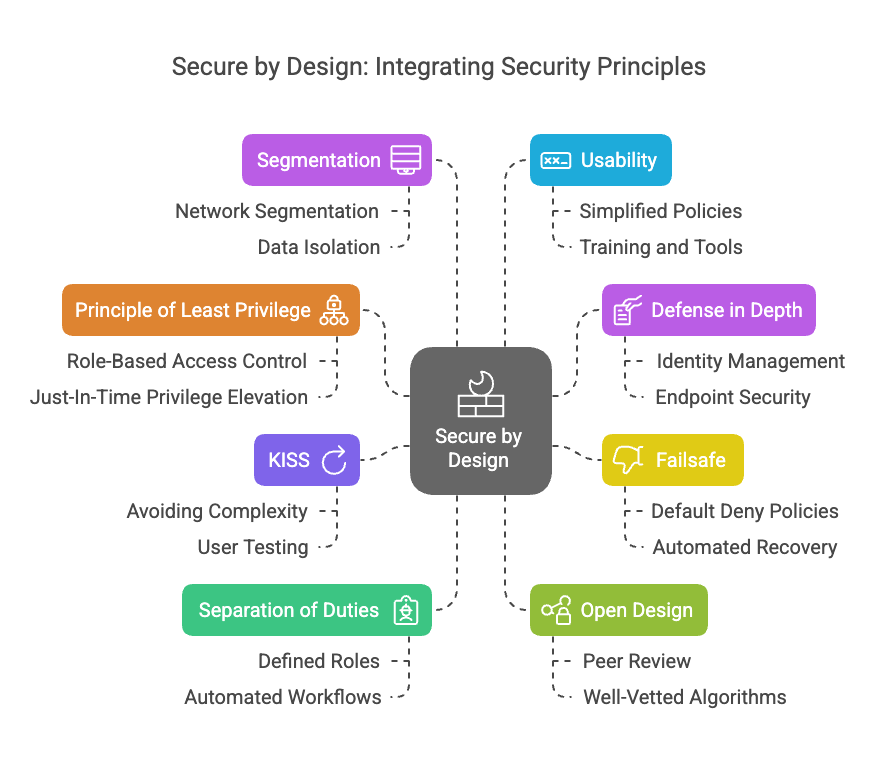
Security by Design Integration principles to identity controls at the foundation level, ensuring that user convenience is layered above security rather than replacing it.
This complexity also affects visibility. Modern environments often contain dozens, sometimes hundreds, of interconnected services. Each integration creates a new data pathway and a potential trust relationship. Without careful architectural oversight, these relationships can become opaque even to the organisations operating them.
The result is an environment where risk is distributed across the system rather than located in a single vulnerability.
Practical Takeaways for Security and Infrastructure Professionals
For practitioners responsible for modern infrastructure, addressing the convenience paradox does not require rejecting usability altogether. Instead, it requires restoring the correct architectural order.
Security and privacy must shape the design of systems before convenience layers are introduced.
Several practical principles consistently support this approach.
Treat identity as core infrastructure
Identity and access management systems are no longer supporting components. They are central security boundaries. Identity architecture should therefore receive the same design attention as networks, compute resources and storage systems.
Reduce implicit trust between services
Architectures based on implicit trust assumptions frequently collapse under scale. Approaches such as Zero Trust aim to remove these assumptions by requiring continuous verification of identity and context before granting access.
Minimise data collection by design
Privacy engineering should begin with a simple question: is this data genuinely necessary? Reducing data collection lowers both privacy exposure and security risk.
Integrate security decisions into system architecture
Security controls are most effective when implemented during design rather than added later. When architecture teams and security teams collaborate early, systems are more resilient and far easier to govern.
| Principle | Purpose | Security Benefit |
|---|---|---|
| Identity as infrastructure | Centralised identity architecture | Reduced credential abuse |
| Zero Trust verification | Continuous authentication checks | Limits lateral movement |
| Data minimisation | Reduce unnecessary data storage | Lower privacy risk |
| Security-first architecture | Embed controls during system design | Stronger long-term resilience |
Closing Reflection
Technology will always evolve toward simplicity. Users expect it, organisations benefit from it and modern infrastructure depends upon it.
However, convenience must remain a design outcome rather than a design driver.
When convenience leads the architecture, security and privacy inevitably become reactive controls. When security and privacy lead the architecture, convenience can still exist - but it exists safely within defined boundaries.
That distinction matters more than it may initially appear.
Convenience optimises systems for the present moment. Security and privacy ensure those systems remain trustworthy in the future.
For organisations designing modern infrastructure, the principle is simple but increasingly important:
Security and privacy should never be sacrificed for convenience.
Sources
IBM (2025) Cost of a Data Breach Report 2025
https://www.ibm.com/reports/data-breach
Verizon (2025) 2025 Data Breach Investigations Report
https://www.verizon.com/business/en-gb/resources/reports/dbir/
Microsoft (2025) Microsoft Digital Defense Report
https://www.microsoft.com/en-us/corporate-responsibility/cybersecurity/microsoft-digital-defense-report-2025/
European Commission (2016) General Data Protection Regulation (GDPR)
https://eur-lex.europa.eu/eli/reg/2016/679/oj


0 Comments