What the MOVEit Breach Still Teaches Us About Security
In cybersecurity, the most damaging incidents rarely begin with sophisticated attacks. More often, they start with something far less dramatic: a trusted system, widely adopted, quietly exposed.
The exploitation of the MOVEit Transfer vulnerability in 2023 is a case in point. What appeared to be a niche file transfer tool quickly became a global incident affecting governments, financial institutions, and critical service providers. According to Reuters, the breach impacted hundreds of organisations and exposed data relating to millions of individuals (National Cyber Security Centre, 2023).
At first glance, this looks like a story about a single vulnerability. It is not.
It is a story about how modern infrastructure is designed, integrated, and prioritised.
MOVEit was not obscure software. It was embedded into workflows precisely because it made data transfer easier, faster, and more reliable. In other words, it solved a business problem efficiently. But that same efficiency introduced a structural risk, centralisation of sensitive data flows through a single, internet-facing service.
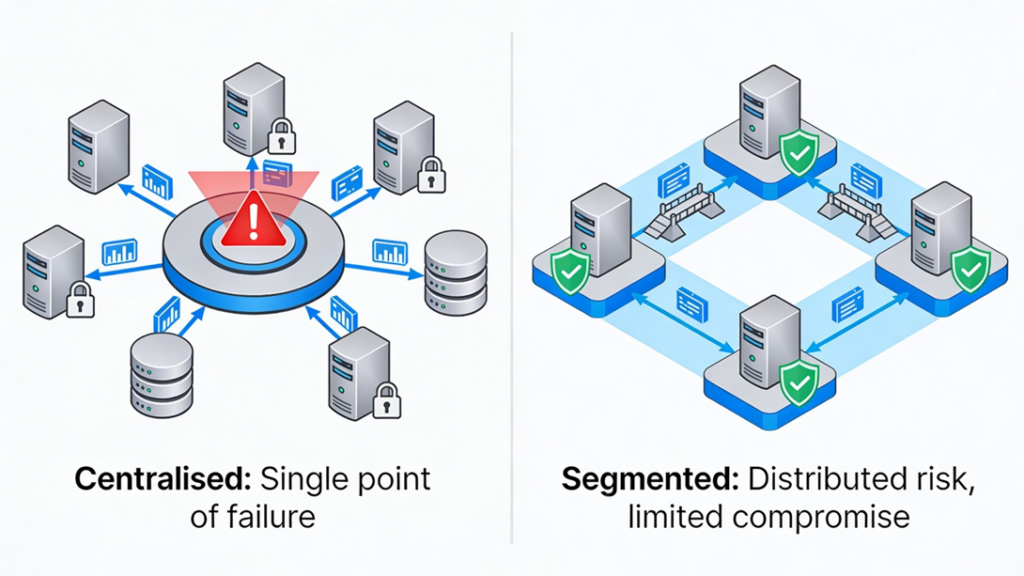
Once a zero-day vulnerability was identified and exploited by the Cl0p ransomware group, the scale of impact was not determined by the sophistication of the exploit, but by the concentration of trust placed in the system. As the UK’s National Cyber Security Centre noted, exploitation campaigns like this succeed because widely deployed services create “single points of systemic risk” (SentinelOne, 2025).
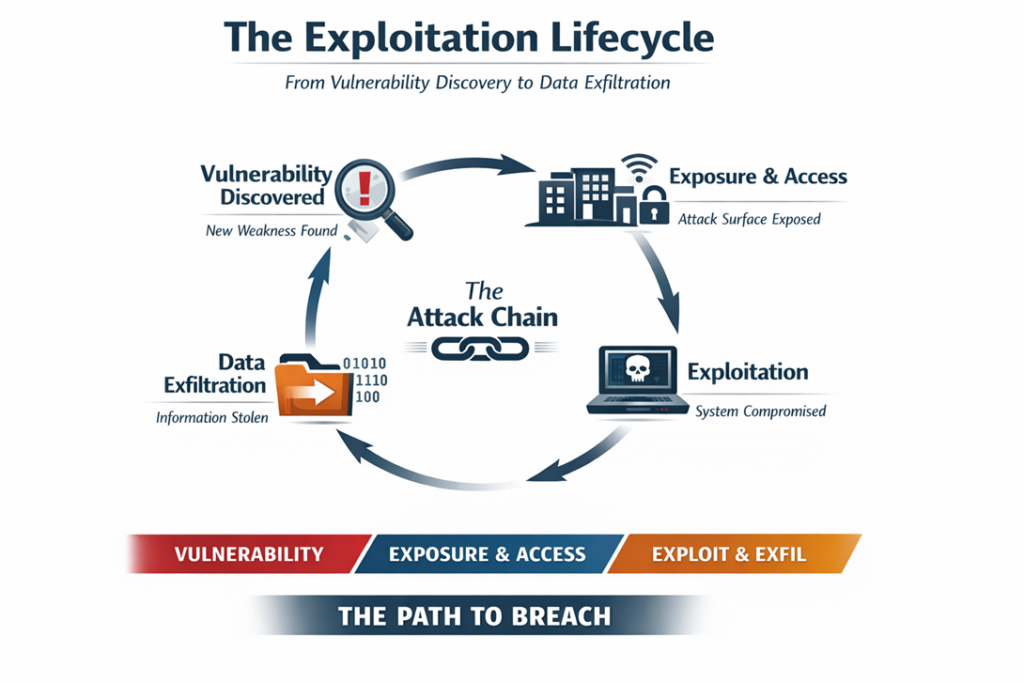
Analysis from Trend Micro highlights that the vulnerability (CVE-2023-34362) enabled unauthenticated access and rapid data exfiltration, reinforcing how quickly exposure can translate into large-scale compromise when internet-facing systems are involved (Trend Micro, 2023).
This is where the conversation needs to shift.
Too often, organisations treat vulnerabilities as isolated technical issues - something to patch, log, and move past. But incidents like MOVEit highlight a deeper issue, architectural dependency combined with operational convenience.
The question is not simply “Was the system vulnerable?” It is “Why was so much trust placed in a system that, if compromised, would expose entire data pipelines?”
From a privacy perspective, the implications are significant. Data transferred through MOVEit often included payroll records, personal identifiers, and sensitive financial information. Once exfiltrated, this data cannot be “patched” in the same way software can. According to IBM’s Cost of a Data Breach Report, data exposure has long-term impacts that extend beyond immediate financial loss, including reputational damage and regulatory scrutiny (IBM, 2025).
This reinforces a principle that is frequently acknowledged but inconsistently applied, security and privacy should never be sacrificed for convenience.
Convenience, in this context, often manifests as:
- Centralised platforms handling large volumes of sensitive data
- Internet-facing services prioritised for accessibility
- Delayed patching due to operational dependencies
- Over-reliance on vendor assurances rather than independent validation
None of these are inherently wrong. In fact, they are often necessary. But without compensating controls, they create predictable attack surfaces. So, what should organisations take away from this?
Table 1: Risk Amplification Factors in Centralised Systems
| Risk Factor | Description | Impact on Incident Severity |
| Centralised Data Flows | Large volumes of sensitive data routed through a single platform | Increases scale of data exposure |
| Internet-Facing Services | Systems accessible externally for operational convenience | Expands attack surface and likelihood of exploitation |
| Vendor Dependency | Reliance on third-party software without independent validation | Limits visibility and control over vulnerabilities |
| Delayed Patch Cycles | Operational constraints slowing remediation | Extends window of exposure |
| High Business Dependency | Critical processes reliant on a single system | Amplifies operational and financial impact |
Table 1 summarises the structural factors that increase the severity of incidents such as MOVEit. These factors do not operate in isolation; rather, they compound one another, creating conditions where a single vulnerability can escalate into a large-scale breach.
First, reduce systemic concentration of risk. Where possible, avoid routing critical data through single platforms without segmentation or redundancy.
Second, treat third-party software as part of your attack surface, not outside it. Vendor trust should not replace internal assurance.
Third, prioritise exposure management over patch management alone. It is not enough to know what is vulnerable; organisations must also understand what is internet-facing, how that exposure manifests, and which systems are both accessible and critical to operations.
Table 2: Exposure vs Vulnerability Management Comparison
| Dimension | Patch Management Focus | Exposure Management Focus |
| Primary Objective | Fix known vulnerabilities | Reduce accessible attack surface |
| Key Question | What is vulnerable? | What is exposed and reachable? |
| Scope | Software and systems | Systems, access paths, and data flows |
| Timing | Reactive (post-identification) | Proactive and continuous |
| Risk Reduction Approach | Remediation | Minimisation of exploitability |
Table 2 highlights the distinction between patch management and exposure management. While patching remains essential, it is insufficient in isolation. A comprehensive security approach requires visibility of both vulnerabilities and the conditions that allow them to be exploited.
Finally, assume that exploitation will happen. The question is not if a vulnerability exists, but how far it can reach when it is exploited.
The MOVEit incident is not an outlier. It is a pattern.
And until organisations address the structural trade-offs between convenience and control, similar incidents will continue to emerge, not as surprises, but as inevitabilities.
Sources
National Cyber Security Centre (NCSC) (2023) MOVEit vulnerability and data extortion incident.
https://www.ncsc.gov.uk/information/moveit-vulnerability
SentinelOne (2024) CVE-2023-34362: Unmasking MOVEit Transfer Vulnerability.
https://www.sentinelone.com/blog/cve-2023-34362-moveit-transfer-vulnerability
SentinelOne (2024) MOVEit Transfer exploited to drop file-stealing SQL shell.
https://www.sentinelone.com/blog/moveit-transfer-exploited-to-drop-file-stealing-sql-shell
Trend Micro (2023) Insights on vulnerabilities in MOVEit Transfer.
https://www.trendmicro.com/en_us/research/23/f/insight-on-vulnerabilities-in-moveit-transfer.html


0 Comments